Operational Resilience for
Edge Compute
Hardware enforced. Software defined.
The US-made resilience stack that keeps unattended edge compute trusted, updatable, and recoverable – for its entire operational life.
Add autonomous security, compliance, and recovery to your edge assets.
Hardware enforced. Software defined.

Trusted by thousands of professionals worldwide

Build Faster. Deploy with Confidence.
No Bricked Devices
Maximize fleet ROI with higher uptime and faster recovery. Automatic rollback and recovery endpoints restore devices to a verifiable state—eliminating costly truck rolls and manual intervention.
Innovation Risk Off
Build on a resilient foundation. Deploy model and OS updates across heterogeneous platforms without disrupting operations or bricking fleets. Integrate resilience at any stage—no costly architectural rewrites required.
Secure & Compliant
Meet NIS2, EU CRA, and other industry standards with hardware-enforced security, self-attestation, and recovery—designed for unattended devices operating long term in zero-trust edge environments.
Resilience Stack
A tightly integrated, easy-to-deploy resilience stack built to secure, update, and recover unattended Linux devices at scale—across their entire lifecycle.
- Secure boot integration.
- File system encryption.
- A/B image partitions with automatic rollback and safe recovery.
- Flexible recovery endpoints and policies for unattended devices.
- Choice of secure hardware that scales to chip level integration.
- APIs for easy integration with applications and XOPs tools.
- Hardware security engine for cryptographic services, key management.
- Physical tamper protection and platform measurement.
Protect Your AI Models
Deliver, run, and update edge AI models frequently without leaking IP or bricking devices. Validate sensor data provenance and guard against model poisoning at runtime.
- Secure, flexible update pipeline enables rapid model evolution.
- Hardware-enforced encryption and precision key management.
- Separate keys for OS, AI models, service access and IO hardware.
- Fully integrated with device recovery and physical tamper defenses.
Robust OS Image Management
- Ultimate flexibility in choosing and deploying Linux OS images. No lock-in to one OS.
- Fully custom images supported (Yocto, Buildroot, etc.)
- Zymbit provides starter images and image customization support
- Zymbit offers turn-key image service to fully manage and test OS images.
- Virtually unlimited flexibility with full security perimeter, secure boot, etc.
Bootware
- Confidence to do OS updates without fear of bricking devices.
- Redundant A/B or A/S images with artifact isolation.
- Native OS switcher with built-in redundancy. No Hypervisor required.
- Full integration with secure boot and Zymbit HSM.
- Bare metal recovery capable HSM for autonomous recovery.
Compute Platform Agnostic
- Architected to work with major Linux compute platforms
- Zymbit designs the entire stack from HSM to Bootware.
- Unmatched quality compared to third-party frameworks.
- Raspberry Pi + Linux + AI accelerators supported as standard.
- Nvidia platforms are supported via image service.
- Custom AI platforms are supported, contact Zymbit.
Hardware Security Engines
- Proven, edge-hardened hardware security for unattended nodes.
- Easy to use, trusted APIs, industry-leading UX.
- Zero trust provisioning – no trusted human required.
- Hardware monitoring: multiple perimeter circuits and power monitoring.
- Self-destruct support and protection while device is powered off.






Get started today
Security Engines
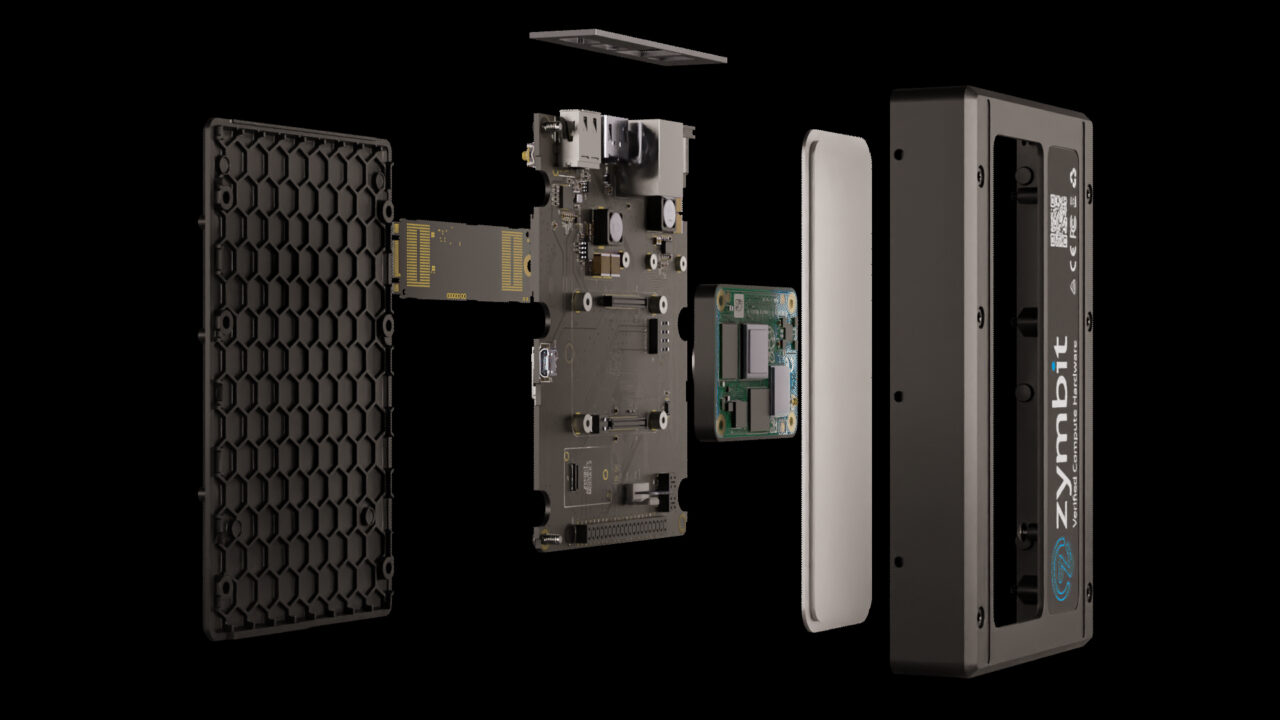
Secure Compute Nodes
Engineering Services
Trusted by professionals worldwide

Loved by developers
Modular software and hardware that scales smoothly as your device security needs grow

Trusted by ops teams
Long term security and reliability managed from your existing ops infrastructure
Built for intelligent edge infrastructure

Drone Infrastructure
protects critical navigation and communication credentials in drones and traffic managers

Autonomous Vehicles
supports encrypted file system, robust OTA updates and self-recovery

On-Prem Key Management
enables application specific cryptographic key management, wallets and services