HSM6

The embedded hardware wallet
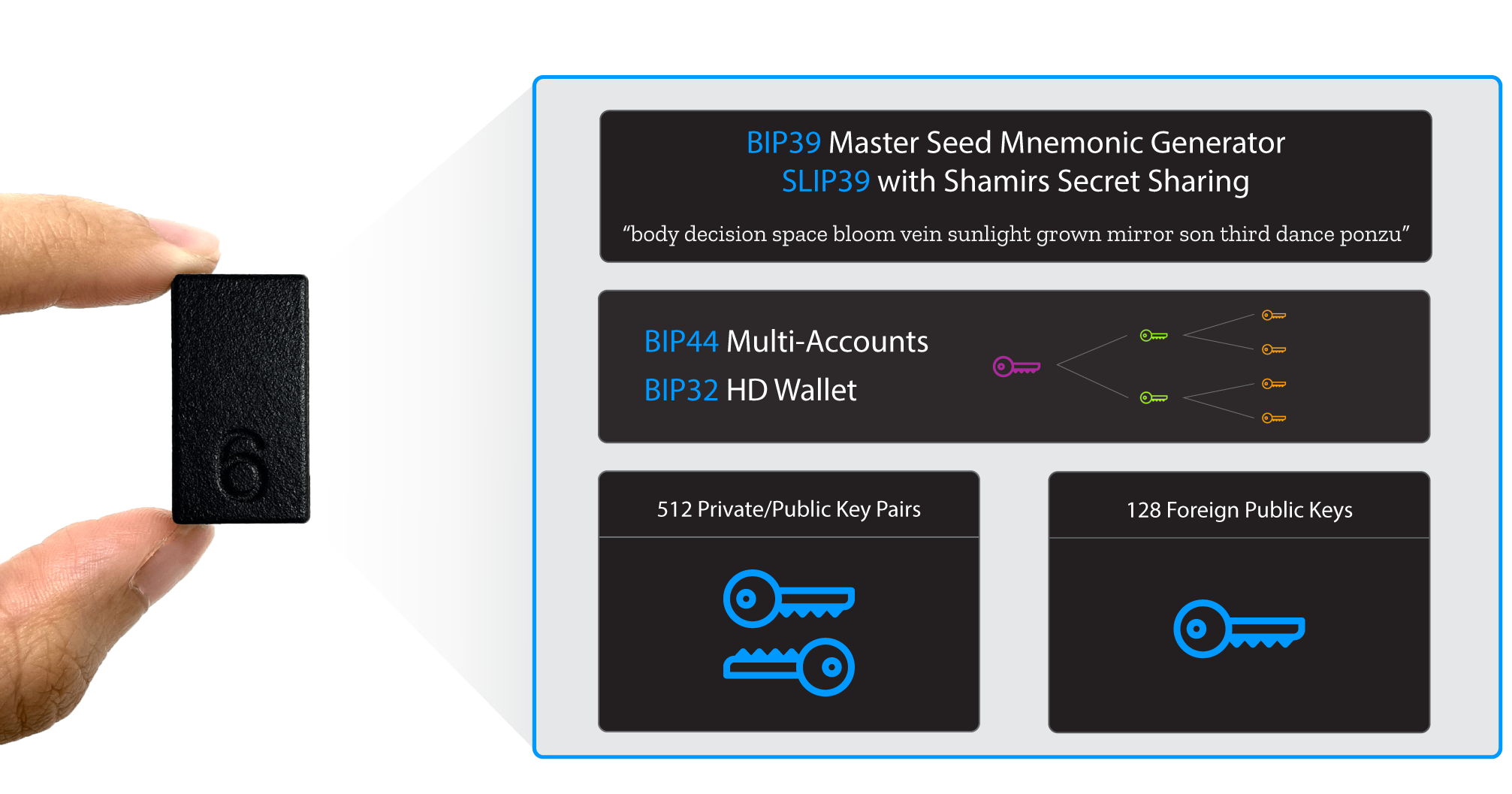
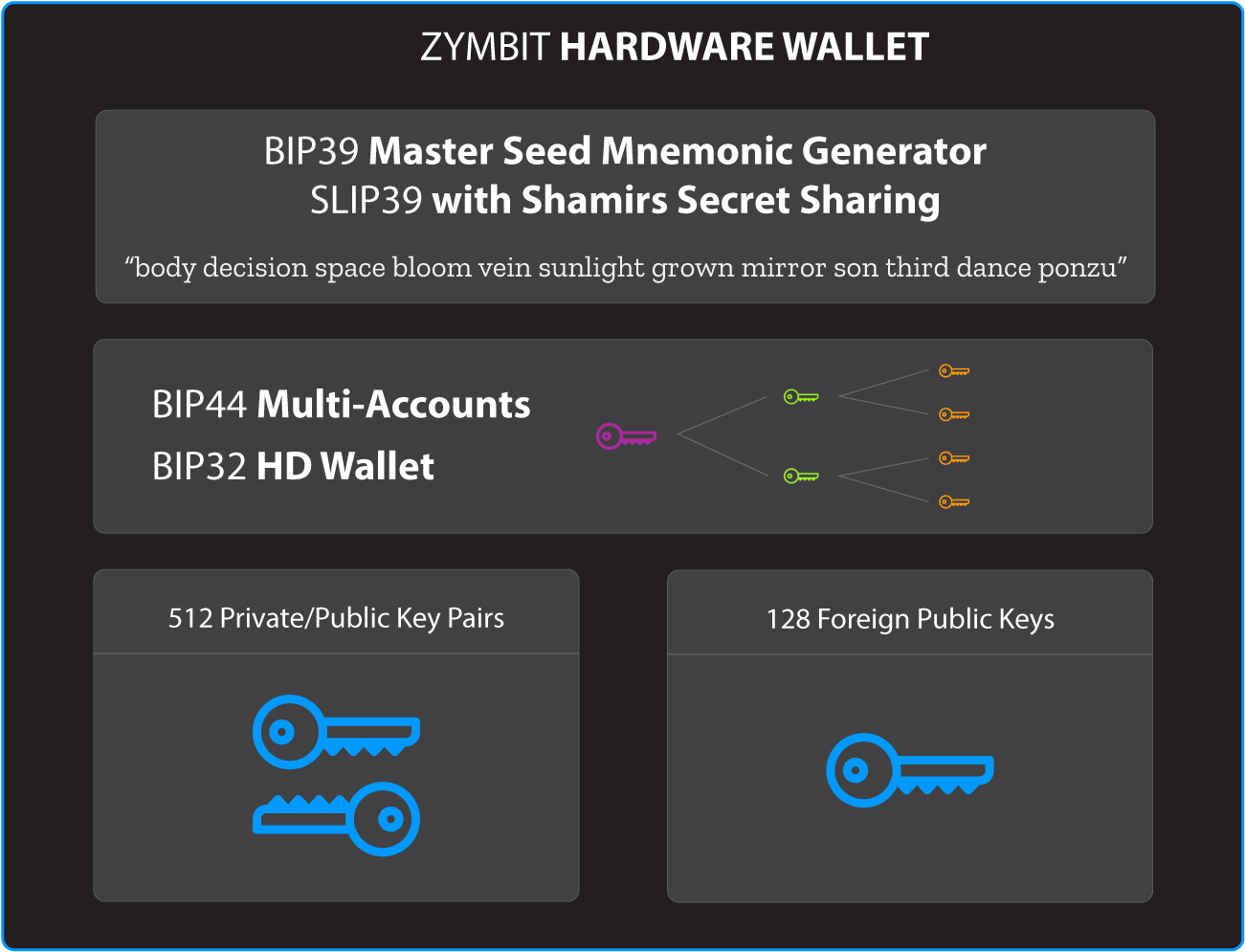
HSM6 is a secure hardware wallet that protects hundreds of keys from physical and digital exploits. HSM6 provides tools for generating, managing and recovering keys using standard BIP and SLIP protocols for hierarchical deterministic (HD) wallets and mnemonic and seed phrase recovery.
HD Wallet
A Hierarchical Deterministic (HD) wallet is a reliable and secure way to manage hundreds of keys, embedded in a single device.
HD wallets use proven de-facto standard algorithms developed for blockchain and crypto applications. Zymbit’s HSM6 product implements standard protocols – BIP32/39/44 and SLIP39 – in a compact, easy to integrate module that’s programmable through secure APIs.
Python, C, C++ APIs
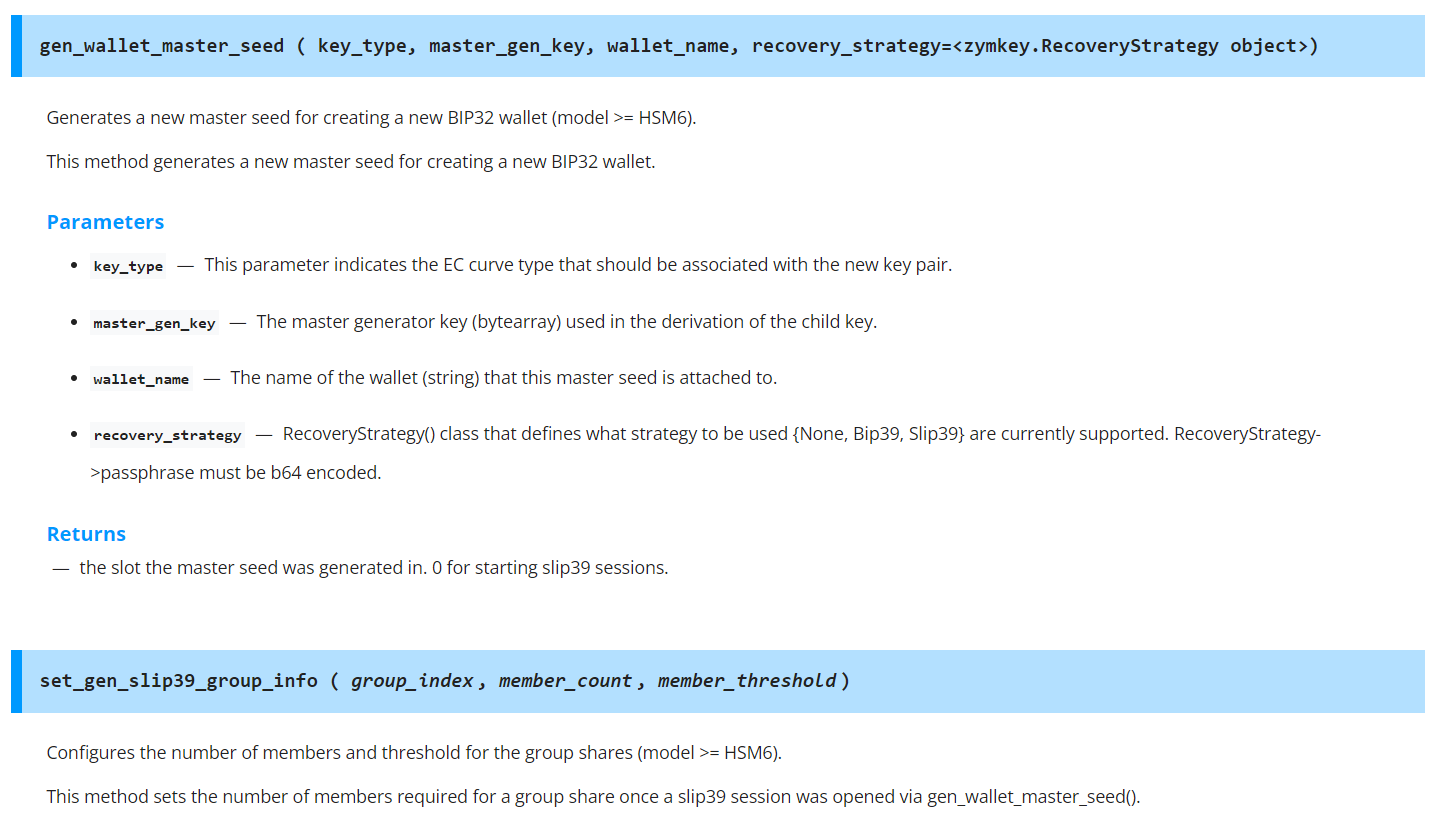
As developers ourselves, we try to build APIs that allow you to benefit from the power of cryptography, without needing to understand the underlying math. Zymbit wallet functions are designed to provide access to powerful features like generating a wallet master seed, child keys and managing wallet recovery from mnemonic phrases and shared secrets.
Send Web3 Ethereum transactions
Signatures play a critical role in ensuring the authenticity and ownership of blockchain transactions. Learn how to integrate Zymbit into your Web3 Ethereum application.
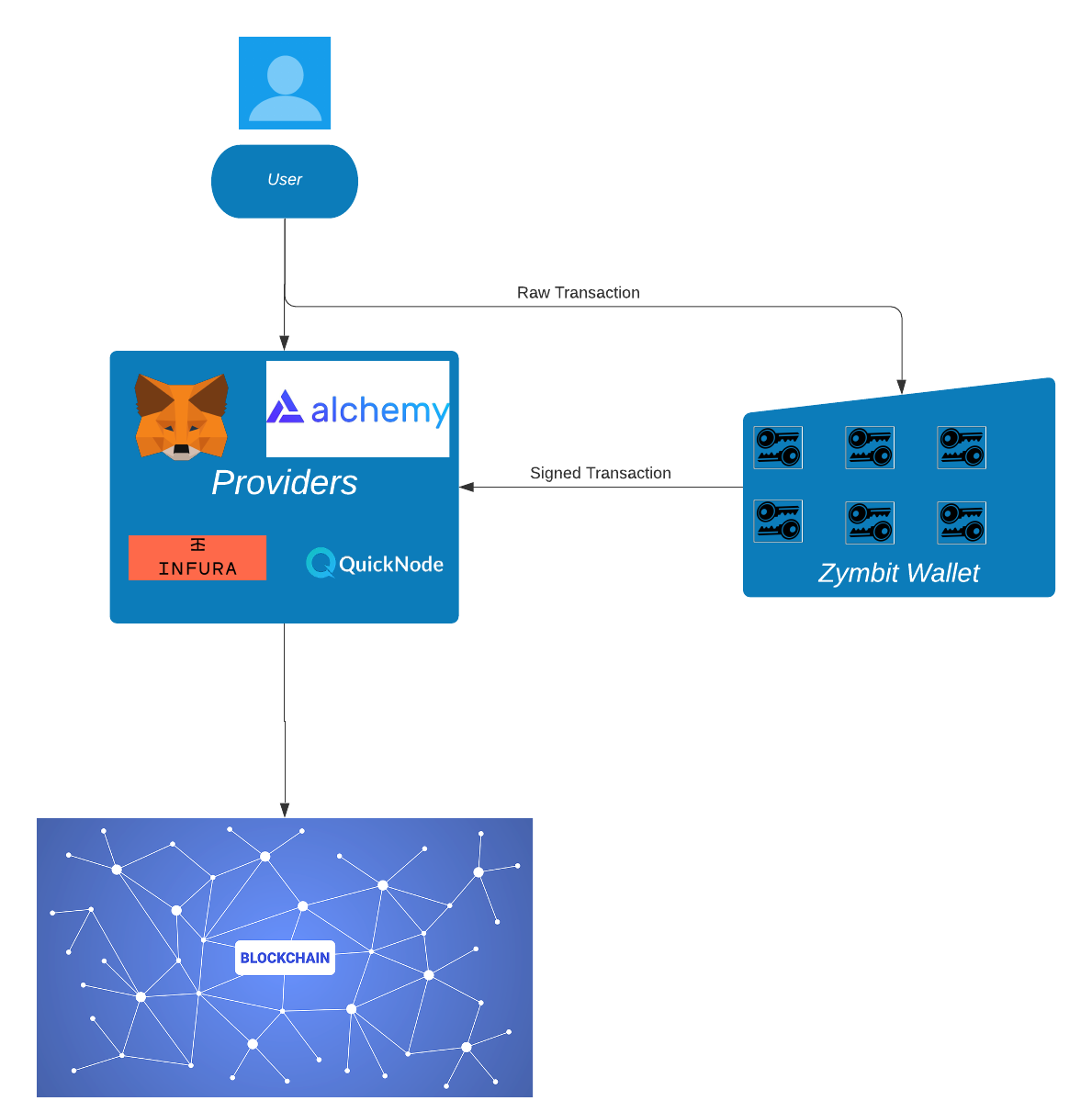
MetaMask Integration Project
We started a new project in summer 2022 to provide a seamless integration of MetaMask with Zymbit HSM6 and SCM products. This is a work-in-progress, and you can join the conversation in MetaMask forum.
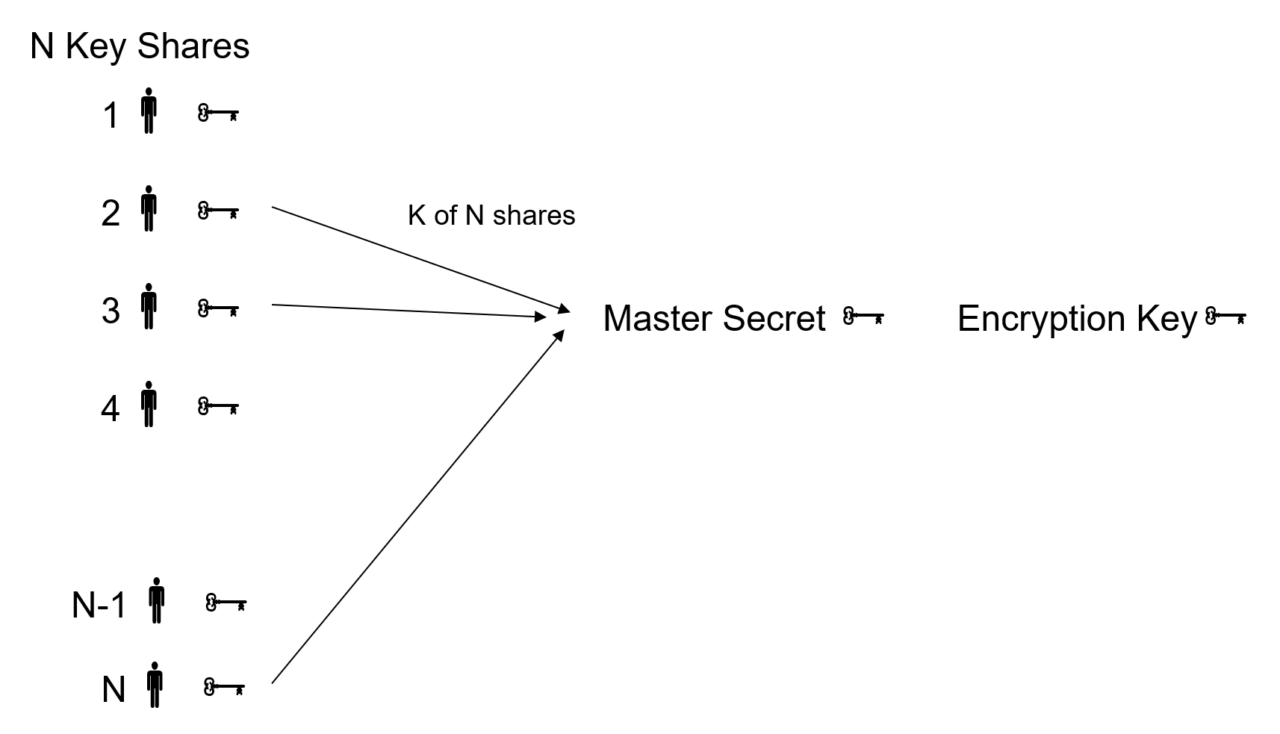
Wallet recovery with SLIP39 Shamir's secret sharing
HSM6 implements SLIP39 from Satoshi Labs. This protocol provides a standard and interoperable implementation of Shamir’s secret-sharing (SSS) that can be used to back up Hierarchical Deterministic Wallets described in BIP-0032. SSS splits a master secret into unique parts which can be distributed among participants. A specified minimum number of parts is required to be supplied in order to reconstruct the original secret. Knowledge of fewer than the required number of parts does not leak information about the master secret.
Read-only oversight wallet
The Zymbit oversight wallet is a read-only wallet that contains only public keys, not their corresponding private keys. This feature can be useful for providing a copy of a wallet to a financial advisor or account supervisor who needs to track the history of a wallet, but should not be able to change it in any way.
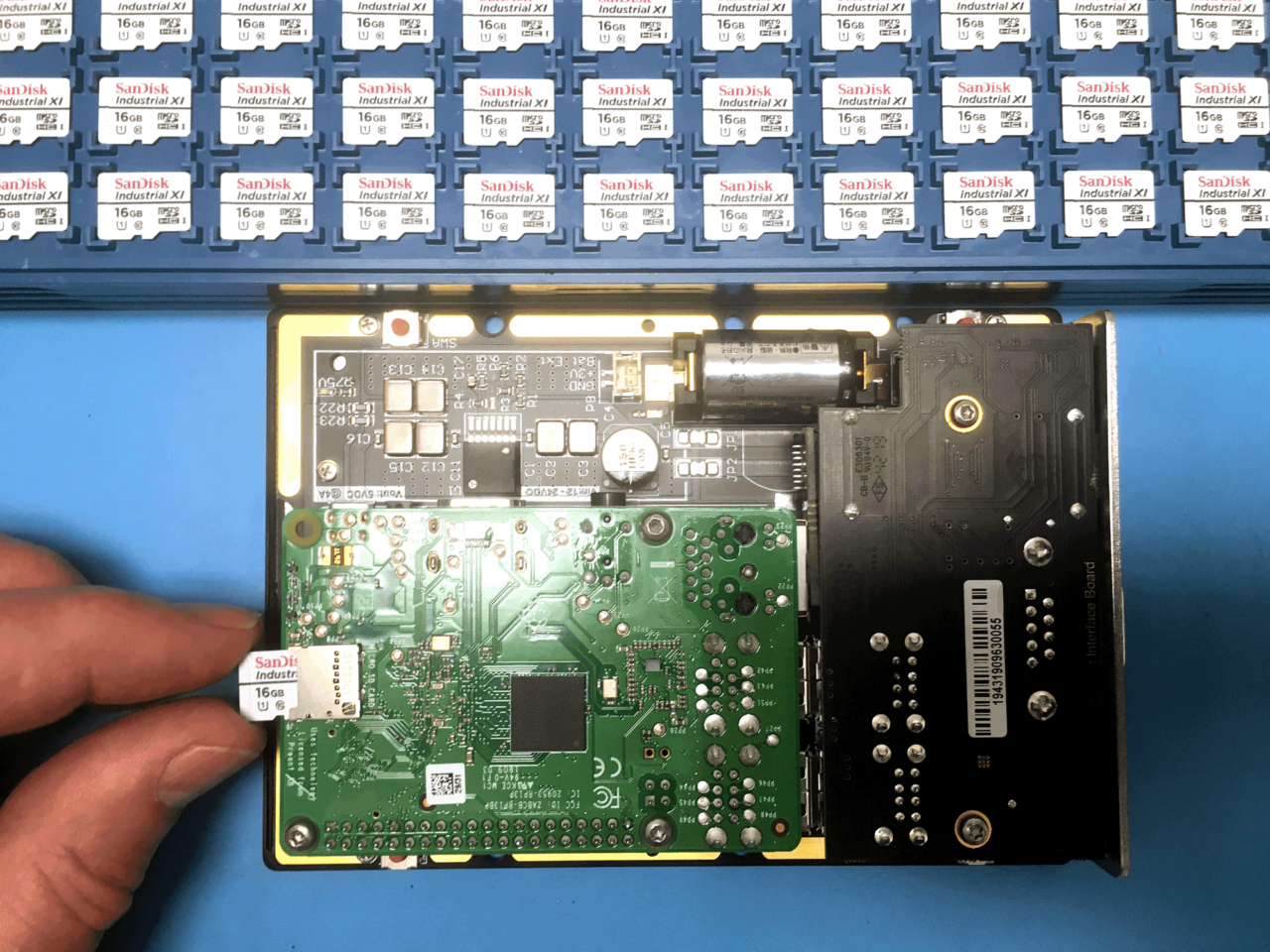
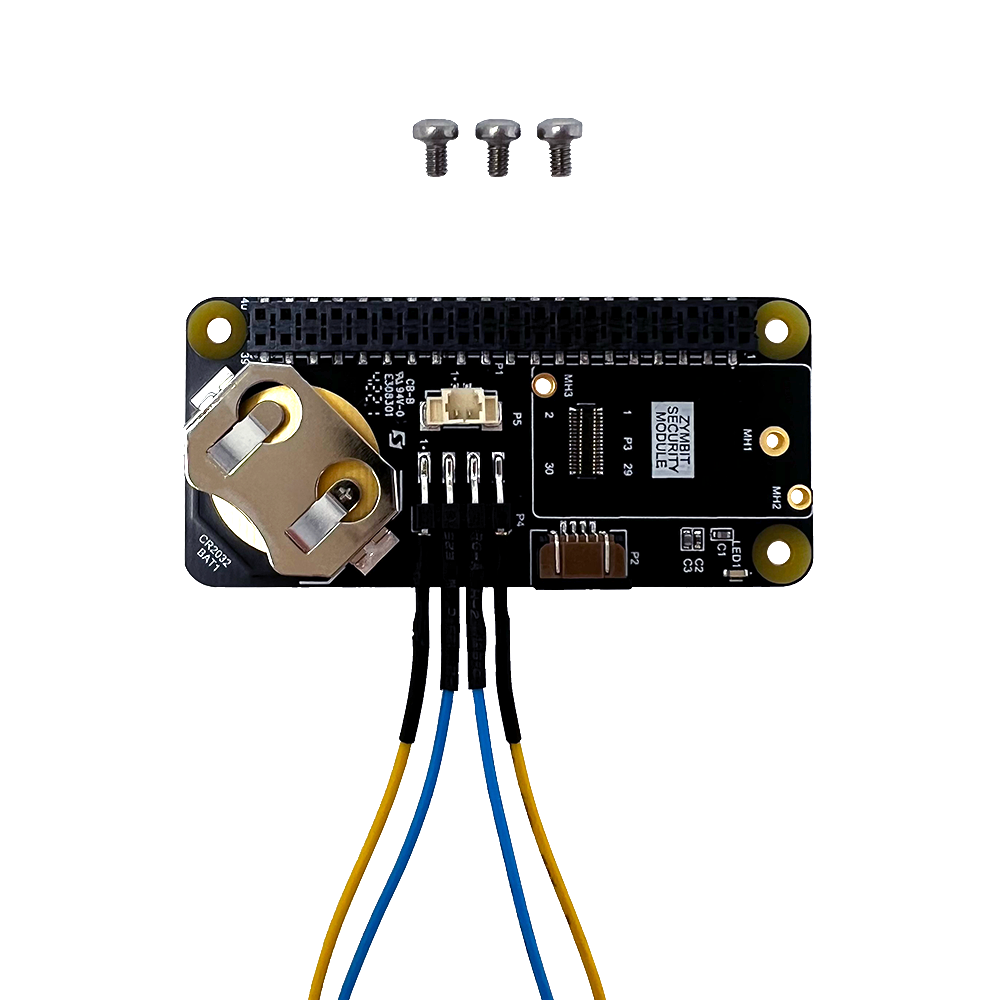
Fully encapsulated module
Developer tools
- The easy way to prototype with HSM6.
- Developer hats compatible with Raspberry Pi, NVIDIA Jetson Nano, NVIDIA Xavier NX.
- CAD files available for motherboard integration.

Manufacturing tools
Zymbit manufacturing tools and services help you transition to volume manufacturing quickly and securely.
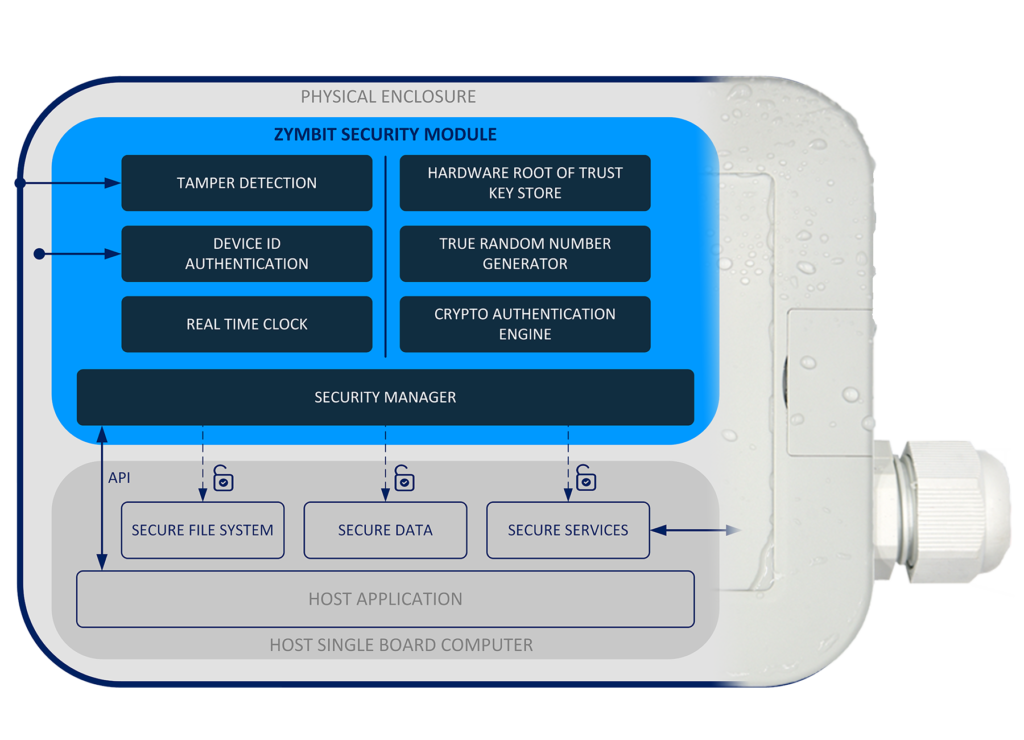
Layered security stack with hardware root of trust
Zymbit security modules provide multiple layers of physical and digital protection for your digital assets, managed through a simple API.
Specifications
| Private / public key pairs | 512 |
| Foreign public keys | 128 |
| Wallet Functions | BIP 32 - hierarchical deterministic wallet BIP 39 - master seed mnemonic generator SLIP 39 - with shamir's secret sharing BIP 44 - mulit-account support |
| Cryptographic Services | ECC KOBLITZ P-256 (secp256k1) ED25519, X25519 ECDH (FIPS SP800-56A) TRNG (NIST SP800-22) ECC NIST P-256 (secp256r1) ECDSA (FIPS186-3) AES-256 (FIPS 197) |
| Tamper Sensors | 2 x Perimeter breach detection circuits Accelerometer shock & orientation sensor Main power monitor Battery power monitor battery removal monitor |
| Software API | Python, C++, C |
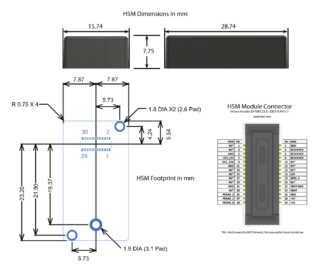
| Physical Format | Encapsulated module |
| Dimensions | 15.7 x 28.7 x 7.8 mm 0.62 x 1.13 x 0.31 Inches |
| Connectors | Module connector: Hirose Header DF40HC(3.5)-30DS-0.4V(51) Mating connector: Hirose Receptacle DF40C-30DP-0.4V(51) |
| Communication | I2C, default address, user changeable GPIO4, user changeable |
| Production mode lock | Software API command |
| Measured system identity & authentication | Standard factors include RPI host, SD card, Zymkey |
| Data encryption & signing applications. | Encrypt root file system with dm-crypt, with LUKS key manager hook Encrypt data blobs with "zblock" function Encrypt data in flight with OpenSSL integration |
| Real time clock | 36-60 months operation with external CR2032, application dependent, 5ppm accuracy. |
| Backup battery | Used for RTC and perimeter circuits External 3V coin cell, eg CR2032 |
| Backup battery monitor | Yes |
| Last Gasp battery removal detection | Yes |
| OEM Custom features | Contact Zymbit |
| Example Cipher Suites | AWS-IOT | TLS_ECDHE_ECDSA_AES256_SHA MS-AZURE | TLS_ECDHE_ECDSA_AES_128_GCM_SHA256_P256 |
| Accessories & related products | Developer Hat |
| Warranty | 18 months |
| Compatibility | Raspberry Pi Zero, 4, 5 |
Documentation
Using Product >
- Getting started
- Software APIs – python, C, C++
- Tutorials
- FAQ & troubleshooting
Conformity Documents >
- EU Declaration of Conformity
- FCC Declaration of Conformity
- RoHS/Reach Declaration of Conformity
- California Prop 65 Declaration of
CAD Files >
- Mechanical dimensions
- Step model
Manufacturing Tools >
- Secure high speed encryption appliance
- Programming and provisioning